Analysis
Security analysis
The first step is always analyze the problem.
Not all organizations are always certain which processes are the most vital or contains the most important assets.
An useful action in that case to perform is a quick process scan to identify those part in an organization which must be a focal point with regard to security.
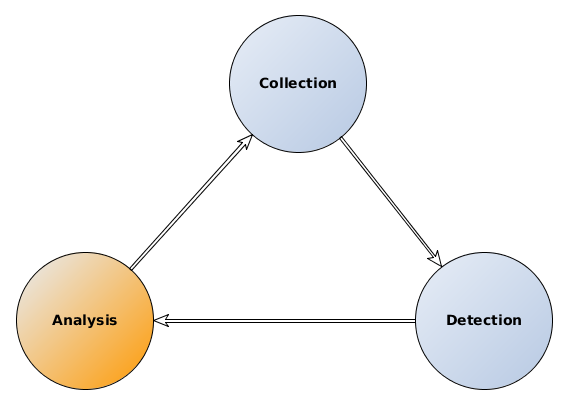
Collection - detection - analysis
 Knowing the vital systems/processes and the principal assets, a vulnerability analysis is the next step.
Knowing the vital systems/processes and the principal assets, a vulnerability analysis is the next step.
Analysis of measures
The hardest step is always translating risk an vulnerabilities in technical measures to counter the known and unknown threads.